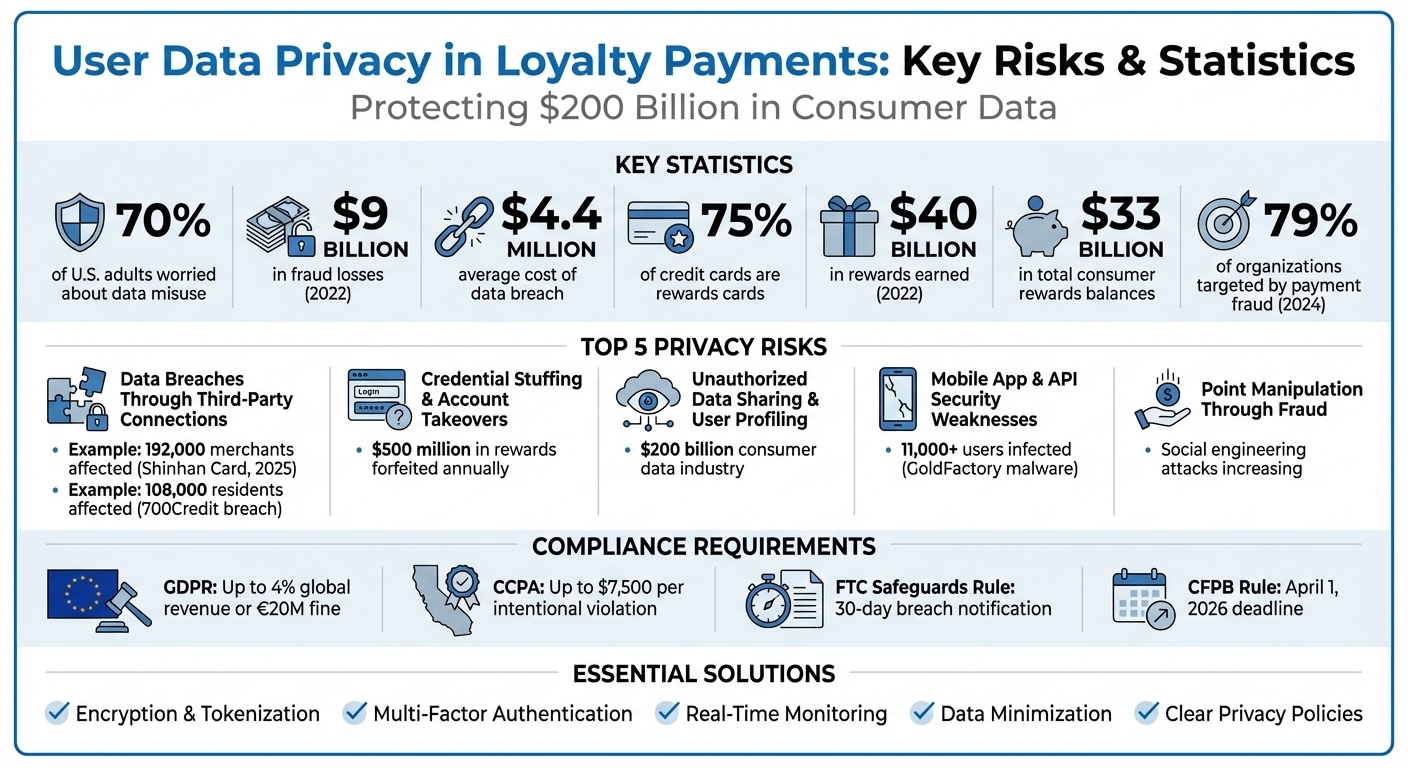
Loyalty programs collect vast amounts of personal data, making them attractive targets for cybercriminals. Businesses face challenges like data breaches, credential theft, and compliance with privacy laws. With 70% of U.S. adults worried about data misuse, and breaches like Caesars Entertainment‘s exposing 65 million records, the stakes are high. Here’s what to know:
- Top Risks: Data breaches, credential stuffing, unauthorized data sharing, and weak API security.
- Consumer Impact: Fraud losses reached $9 billion in 2022, with loyalty accounts increasingly targeted.
- Solutions: Encryption, multi-factor authentication, real-time monitoring, and compliance with laws like GDPR and CCPA.
- Key Example: Platforms like meed offer tools to secure loyalty programs, helping businesses protect data while meeting legal requirements.
Protecting user data is about more than avoiding penalties – it’s about maintaining trust in a $200 billion consumer data industry.
Loyalty Program Data Privacy Risks and Statistics 2025
What Data Privacy Rules Apply To Loyalty Programs?
Main Privacy Risks in Loyalty Payment Systems
Loyalty payment systems come with their own set of security challenges, putting customer data at risk. Understanding these vulnerabilities is essential to safeguarding both your business and your customers. Let’s break down the major risks and explore how they can impact loyalty programs.
Data Breaches Through Third-Party Connections
Loyalty programs often rely on third-party services like payment gateways, databases, or plugins to function. While these integrations are necessary, they also create opportunities for attackers to exploit weak points in the system.
For example, unsecured APIs and web applications can be vulnerable to injection attacks, where hackers insert malicious code to access sensitive data. Similarly, outdated plugins or software that haven’t been patched with the latest security updates can become easy targets for automated attacks. Even something as simple as failing to change default passwords on new hardware, like PIN pads or routers, can give attackers a direct way in.
One high-profile example is the 2025 data breach at Shinhan Card in South Korea, which affected 192,000 merchants. This incident highlighted how flaws in third-party connections can compromise vast amounts of user data.
Credential Stuffing and Account Takeovers
Account takeovers (ATOs) have become a major issue for loyalty programs. Fraudsters use stolen credentials from previous data breaches to access user accounts, often through a method called credential stuffing. This involves testing large sets of stolen username-password combinations across multiple platforms.
Once inside, attackers can drain loyalty points, make unauthorized purchases, or harvest personal data. They often start with small test transactions to confirm account access before escalating to larger fraud.
The stakes are particularly high for loyalty programs, given their popularity. By the end of 2022, 75% of all general-purpose credit cards were rewards cards, and consumers earned more than $40 billion in rewards that year – a sharp increase from 2019. With total consumer rewards balances exceeding $33 billion, loyalty accounts have become lucrative targets for cybercriminals.
The rise in consumer complaints about disappearing points underscores the growing threat. The Consumer Financial Protection Bureau has noted an increase in users reporting unauthorized access to their accounts, often leading to significant losses.
Unauthorized Data Sharing and User Profiling
Loyalty programs collect a wealth of customer data, from purchase histories to personal identifiers. While this data helps businesses personalize customer experiences, it also raises privacy concerns when shared without proper consent.
The consumer data industry is valued at over $200 billion, making this information highly sought after by data brokers and marketers. Businesses may share user data with third parties, often without customers fully understanding the extent of these practices.
Without strict data-sharing agreements in place, sensitive customer information can end up in the hands of companies users never intended to interact with. As the Consumer Financial Protection Bureau warns, fine print or vague disclosures may not be enough to address these concerns.
Mobile App and API Security Weaknesses
Mobile apps are another vulnerable point for loyalty programs. Fraudulent apps that mimic legitimate ones can trick users into downloading malware, as seen in the GoldFactory malware campaign, which infected over 11,000 users in Southeast Asia.
APIs, which facilitate communication between apps and servers, are also at risk. API misconfigurations can allow attackers to bypass authentication or execute malicious commands. For example, lacking proper encryption (like TLS) for API calls can let attackers intercept sensitive data as it travels between the app and server.
A notable example occurred in December 2025, when 700Credit reported a breach affecting over 108,000 South Carolina residents. The breach stemmed from vulnerabilities in their web application, which allowed unauthorized access to customer records.
Additionally, some mobile apps request over-privileged permissions, accessing data or device functions beyond what’s necessary. If these apps are compromised, the extra permissions can lead to significant data exposure.
Point Manipulation Through Fraud and Social Engineering
Not all attacks rely on technical expertise. Fraudsters frequently use social engineering to manipulate both users and customer service representatives. For instance, phishing emails can trick users into revealing login credentials by mimicking official loyalty program communications.
Fraudsters also exploit program loopholes, such as referral bonuses, to artificially inflate their point balances. In some cases, they create fake accounts or convince customer service teams to transfer points or reset credentials.
These schemes not only hurt businesses financially but also damage user trust. Each year, approximately $500 million in rewards are forfeited, often due to account issues or program changes. When users lose confidence in a loyalty program’s security, they’re less likely to participate or share their data.
"A financial institution’s information security program is only as effective as its least vigilant staff member." – Federal Trade Commission
The combination of weak technical safeguards and human vulnerabilities creates a complex threat landscape that demands robust security measures.
Solutions for Protecting User Privacy
Addressing privacy risks requires businesses to implement strong measures like encryption, authentication, and clear policies to safeguard user data.
Using Encryption and Secure Integration Methods
Encryption is a cornerstone of data protection. It converts sensitive information into unreadable code that only authorized parties can access. Businesses should use symmetric encryption for internal storage, where the same key encrypts and decrypts data, and asymmetric encryption for higher-security scenarios, which relies on public and private key pairs. The private key remains confidential, enhancing security.
"Encryption protects sensitive customer data and financial transactions from unauthorised access, tampering and theft." – Stripe
Securing data during transmission is just as important. Using Transport Layer Security (TLS) protocols ensures that data traveling between customers and servers is protected from interception.
Another effective method is tokenization, which replaces sensitive data with non-sensitive tokens. Even if attackers obtain these tokens, they cannot extract the original data, as it remains securely stored. This also simplifies compliance with PCI DSS requirements.
Failing to protect data can lead to severe financial and legal consequences. Proactively investing in privacy and security measures – such as during the design of loyalty programs – can save businesses from costly repercussions down the line.
"Investing in privacy and security proactively when designing a loyalty program can save businesses from these costly repercussions." – Hannah Ji-Otto, Privacy and Security Attorney, Baker Donelson
Additional measures, like network segmentation, can isolate loyalty payment systems from other business systems, reducing the impact of potential breaches. Coupling this with secure payment gateways ensures a protected channel between customers, businesses, and financial institutions.
To strengthen defenses further, businesses should store encryption keys separately, keep systems updated with regular patches, and conduct periodic vulnerability scans. In 2024, 79% of organizations reported being targeted by payment fraud, with the average global cost of a data breach reaching $4.4 million. These numbers emphasize that prevention is far more cost-effective than dealing with the aftermath.
These technical measures serve as the foundation for additional steps, such as user authentication and monitoring.
Adding Multi-Factor Authentication and Real-Time Monitoring
While encryption protects data, verifying user identity and monitoring activity are essential for a comprehensive security strategy.
Passwords alone are no longer sufficient. Multi-factor authentication (MFA) requires users to verify their identity through at least two factors: something they know (password), something they have (a phone or security token), or something they are (biometric data).
"A good approach to identity and access management will make it hard for attackers to pretend they are legitimate, whilst keeping it as simple as possible for legitimate users to access what they need." – NCSC
MFA significantly reduces the risk of password-based attacks like credential stuffing and brute-force attempts. For accounts with elevated privileges, more robust methods such as hardware security tokens are recommended.
Real-time monitoring adds another layer of protection by identifying suspicious activity, such as failed MFA attempts, unusual logins, or password spraying. Linking every action to a specific user or token improves accountability.
The FTC Safeguards Rule mandates that covered entities notify the FTC within 30 days of discovering a breach involving 500 or more consumers’ unencrypted data. Real-time monitoring can help businesses identify and address potential issues before they escalate. Additionally, having a written incident response plan that outlines roles and procedures can mitigate risks. Using separate accounts for routine activities versus administrative functions also limits exposure to phishing attacks.
Following Privacy Laws and Maintaining Clear Policies
Compliance with privacy laws is not just a legal obligation – it’s also critical for earning customer trust. The General Data Protection Regulation (GDPR) applies to any organization handling the personal data of EU residents, regardless of its location. Non-compliance can result in fines of up to 4% of global annual revenue or €20 million (approximately $21.8 million), whichever is higher.
In the U.S., the California Consumer Privacy Act (CCPA) grants California residents control over their personal data. It applies to for-profit businesses operating in California with annual gross revenues of $25 million or more. Penalties for intentional violations can reach $7,500 per incident, while unintentional violations may cost $2,500 each. Data breaches can also result in civil damages of up to $750 per affected consumer per incident.
The FTC Safeguards Rule, part of the Gramm-Leach-Bliley Act, requires financial institutions to implement a written information security program and enforce MFA for accessing customer data.
"The data collected through loyalty programs (think: emails, purchase histories, demographics, behavioral patterns) falls squarely within the scope of consumer data protection laws." – Jodi Daniels, Founder and CEO, Red Clover Advisors
In early 2024, the Federal Trade Commission issued settlement orders against Marriott International and its subsidiary Starwood for lapses in loyalty program management. These orders required a robust information security program, data minimization practices, and a system for customers to request deletion of their loyalty account data.
Data minimization – collecting only the information essential to a loyalty program’s functionality – can reduce both liability and customer concerns. Approximately 86% of consumers report growing worries about their data privacy.
To ensure compliance, businesses should designate a qualified individual to oversee their security program, encrypt data both at rest and in transit, and establish contracts with third-party vendors that include security expectations and periodic monitoring. Customer data should be securely disposed of within two years of its last use, using methods like "wiping" for electronic media or shredding for physical records.
GDPR requires breach notifications to authorities within 72 hours, while the FTC Safeguards Rule allows 30 days for breaches involving 500 or more consumers. Having clear policies and procedures in place ensures businesses can meet these deadlines efficiently when time is of the essence.
sbb-itb-94e1183
How meed Protects User Data in Loyalty Programs
meed combines strong security measures with seamless loyalty program management, tackling privacy concerns head-on with built-in safeguards available across all subscription levels.
Security Features in meed’s Plans
To address potential risks, meed provides tailored solutions that secure every aspect of loyalty program transactions.
The platform employs encryption and real-time monitoring to protect user data, whether it’s in transit or stored. These measures align with the technical standards required by regulations such as the FTC Safeguards Rule.
One standout feature is disposable identity creation, which lets users generate temporary contact details with a single click. This allows customers to join loyalty programs without revealing their actual personal information. Businesses gain higher engagement rates, while users maintain control over their privacy.
Additionally, data exposure controls empower users to decide exactly what information they share and with whom. This transparency directly addresses concerns about unauthorized data sharing that often plague loyalty programs. Even better, meed’s analytics dashboard – available in all plans, including Starter (free), Pro ($490/year), and Enterprise (custom pricing) – provides businesses with valuable insights while respecting user privacy.
Meeting Compliance Requirements with meed
Beyond its security capabilities, meed is designed to ensure compliance with U.S. privacy regulations through its architecture.
The platform enforces strict data minimization practices, adhering to U.S. privacy standards.
It also features standardized API access that meets current CFPB requirements, including the Personal Financial Data Rights rule. This rule mandates machine-readable developer interfaces with a 99.5% minimum response rate. For businesses, this means they can prepare for the April 1, 2026 compliance deadline for larger institutions without needing to overhaul their systems.
meed also simplifies contractor oversight by maintaining high security standards. Its monitoring systems detect anomalies quickly, ensuring breaches are addressed promptly.
Conclusion
Loyalty programs are great for boosting customer engagement, but they come with serious risks to user data. Breaches, credential stuffing, unauthorized profiling, and weak API security can expose sensitive information. High-profile incidents, like those involving Caesars Entertainment and Dickey’s Barbecue Pit, highlight just how severe these risks can be. These cases underline the urgent need for strong security measures.
To tackle these challenges, businesses should focus on essential practices like encryption, multi-factor authentication (MFA), data minimization, and clear privacy policies. At the same time, they must navigate a growing web of regulations. With 19 U.S. states enforcing comprehensive privacy laws and the CFPB’s Personal Financial Data Rights rule set to take effect on April 1, 2026, for larger institutions, staying compliant is more important than ever.
"Ensuring robust privacy and security measures from the beginning not only protects the business from potential legal and financial fallout but also maintains consumer trust, a vital asset for any loyalty program’s success." – Hannah Ji-Otto, Privacy and Security Attorney, Baker Donelson
Platforms like meed demonstrate how to implement these safeguards effectively. By integrating advanced security protocols – such as encryption, MFA, and secure integrations – meed helps businesses meet regulatory requirements while offering personalized rewards. This allows companies to focus on building engagement rather than worrying about compliance deadlines.
Ultimately, protecting user data isn’t just about avoiding legal troubles. It’s about maintaining the trust that makes loyalty programs successful in the first place. With the consumer data collection industry now valued at over $200 billion, businesses that prioritize privacy will stand out in an increasingly cautious market.
FAQs
How can businesses protect customer data in loyalty programs?
To safeguard customer data in loyalty programs, businesses should embrace a privacy-by-design strategy. This means only collecting the information absolutely necessary for the program and securing explicit consent from participants. Protect this data using robust encryption – both when it’s stored and while it’s being transmitted. For sensitive details like payment information, tokenization adds an extra layer of security.
It’s equally important to control who has access to this data. Implement role-based permissions, require multi-factor authentication, and conduct regular reviews of accounts with elevated access to ensure only authorized personnel can reach sensitive information. Routine security audits, vulnerability scans, and penetration testing are essential to spot and address potential weak points before they can be exploited. And if a breach does occur, a well-prepared incident-response plan can help detect, notify, and resolve issues quickly, minimizing harm and maintaining customer trust.
Tools like meed make data protection easier by offering built-in features such as end-to-end encryption, tokenized reward balances, and centralized data management. These capabilities allow businesses to enforce consistent privacy practices, streamline compliance efforts, and reduce the risk of data breaches – all while boosting customer confidence in the program.
What are the best ways to protect user data in loyalty payment systems?
Protecting user data in loyalty payment systems demands a mix of robust security measures and smart practices to keep sensitive information – like personal details and payment data – safe. Some essential strategies include encrypting data during transfer and storage, tokenizing sensitive details (like card numbers), and using multi-factor authentication (MFA) for all access points. To minimize risks, access should be restricted through role-based controls and by following the principle of least privilege, which ensures users only have access to what they absolutely need.
Regular security audits, vulnerability scans, and secure development practices are vital for spotting and addressing potential weak spots. Adhering to standards like PCI DSS ensures businesses comply with stringent data protection rules, which cover areas like secure password policies, real-time system monitoring, and incident response planning. Moreover, privacy-focused approaches – such as data minimization and routine risk assessments – help ensure only the necessary data is collected and retained.
Platforms like meed incorporate these protections, offering tools like end-to-end encryption, tokenized loyalty balances, and secure administrative features. These measures not only safeguard user data but also improve trust and the overall experience for businesses and their customers.
Why is it important for loyalty programs to comply with privacy laws?
Compliance with privacy laws is an essential aspect of running loyalty programs. It plays a key role in protecting customer trust, avoiding hefty legal penalties, and preserving a positive brand image. These laws are designed to ensure that personal data is handled responsibly – covering how it’s collected, stored, and used – while safeguarding it from potential misuse or security breaches.
When businesses follow privacy regulations, they show a clear commitment to respecting their customers’ rights. This not only builds stronger relationships but also encourages greater loyalty. On the flip side, failing to comply can lead to severe fines and cause lasting harm to both a company’s finances and its reputation.
